A System to Detect Sudden Epileptic Attacks Using Radio Frequency Technology | Project Ideas for BME - YouTube
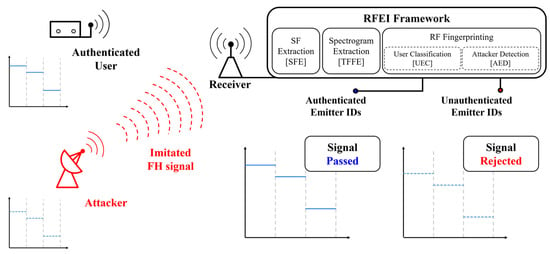
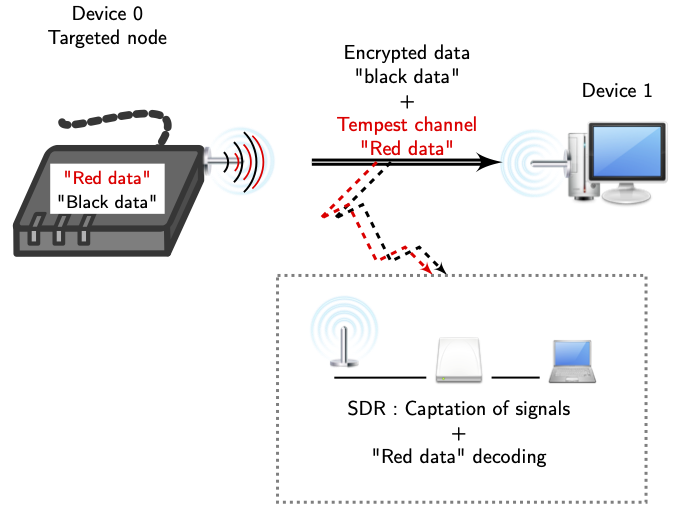
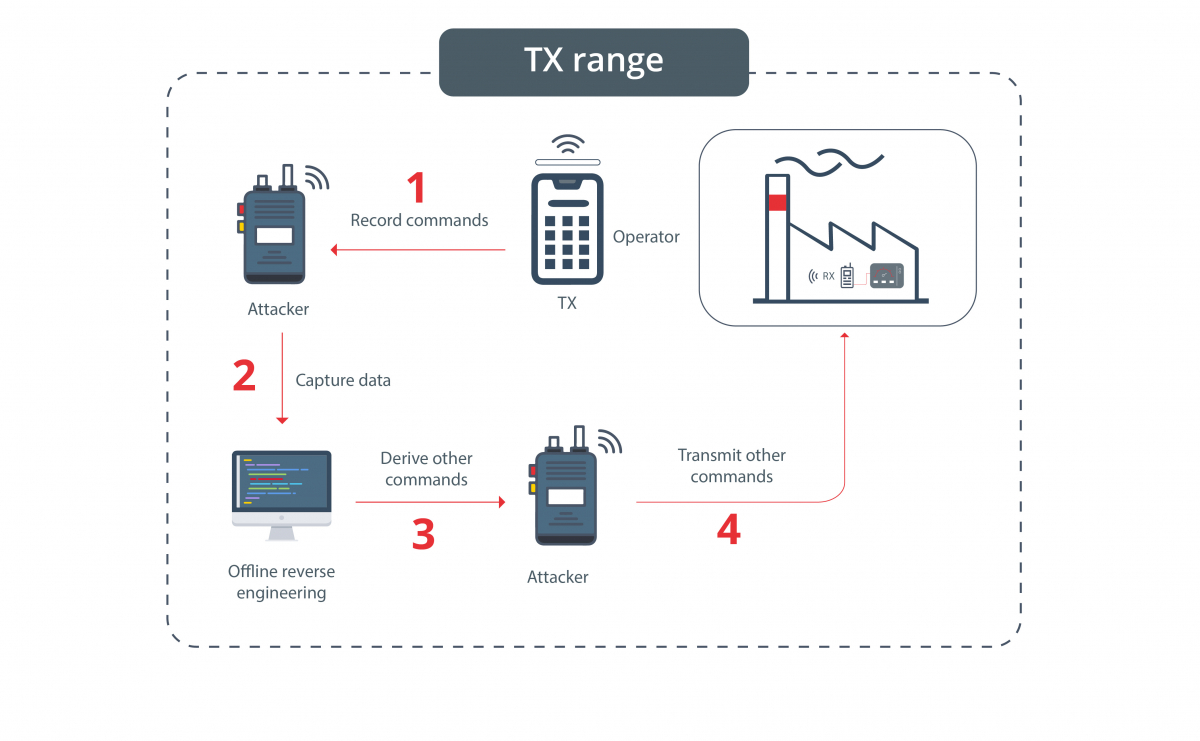
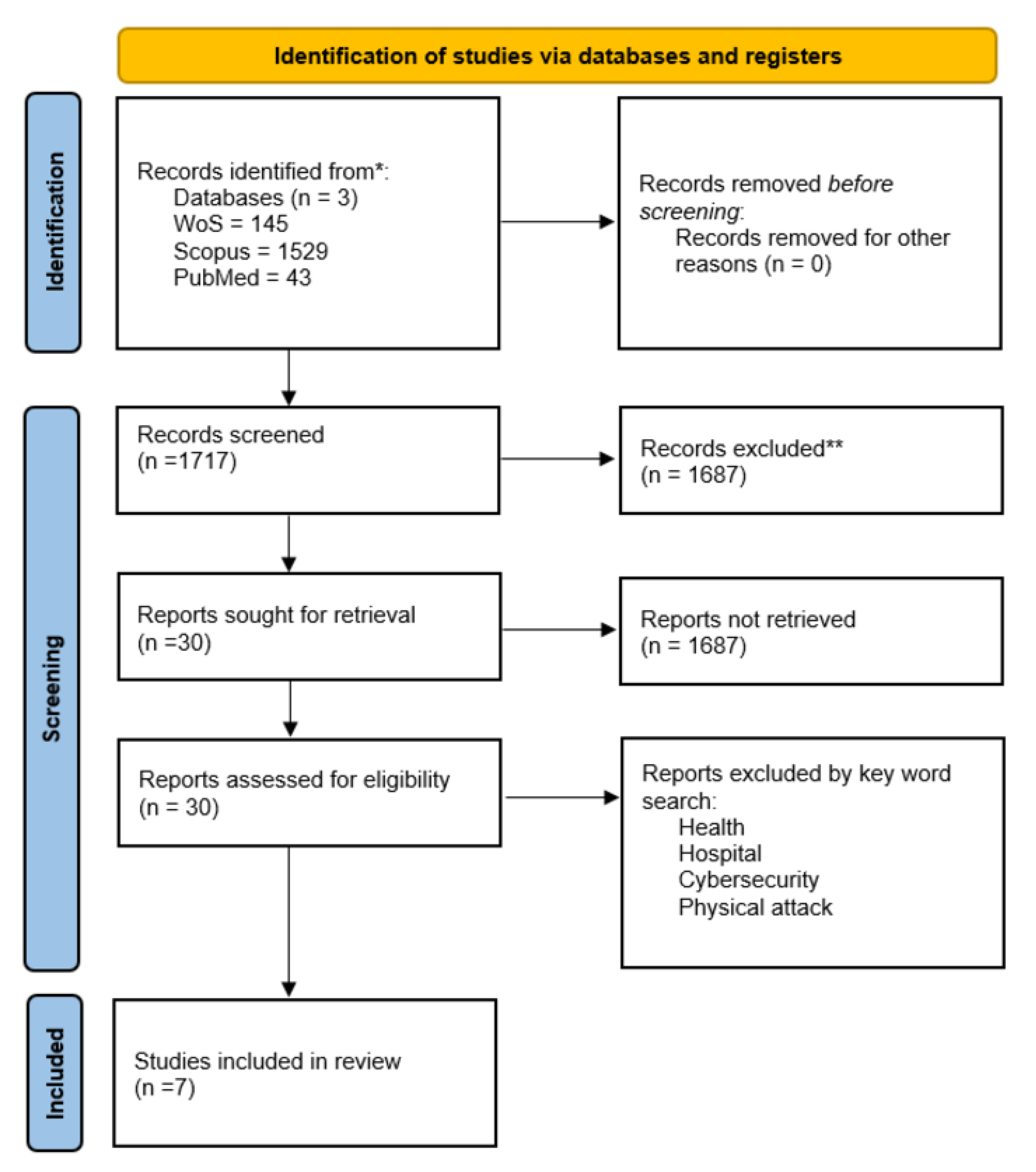
Applied Sciences | Free Full-Text | Radio Frequency Fingerprinting for Frequency Hopping Emitter Identification
Radio Frequency Operations and Training From a Virtually Different Point of View - United States Cybersecurity Magazine
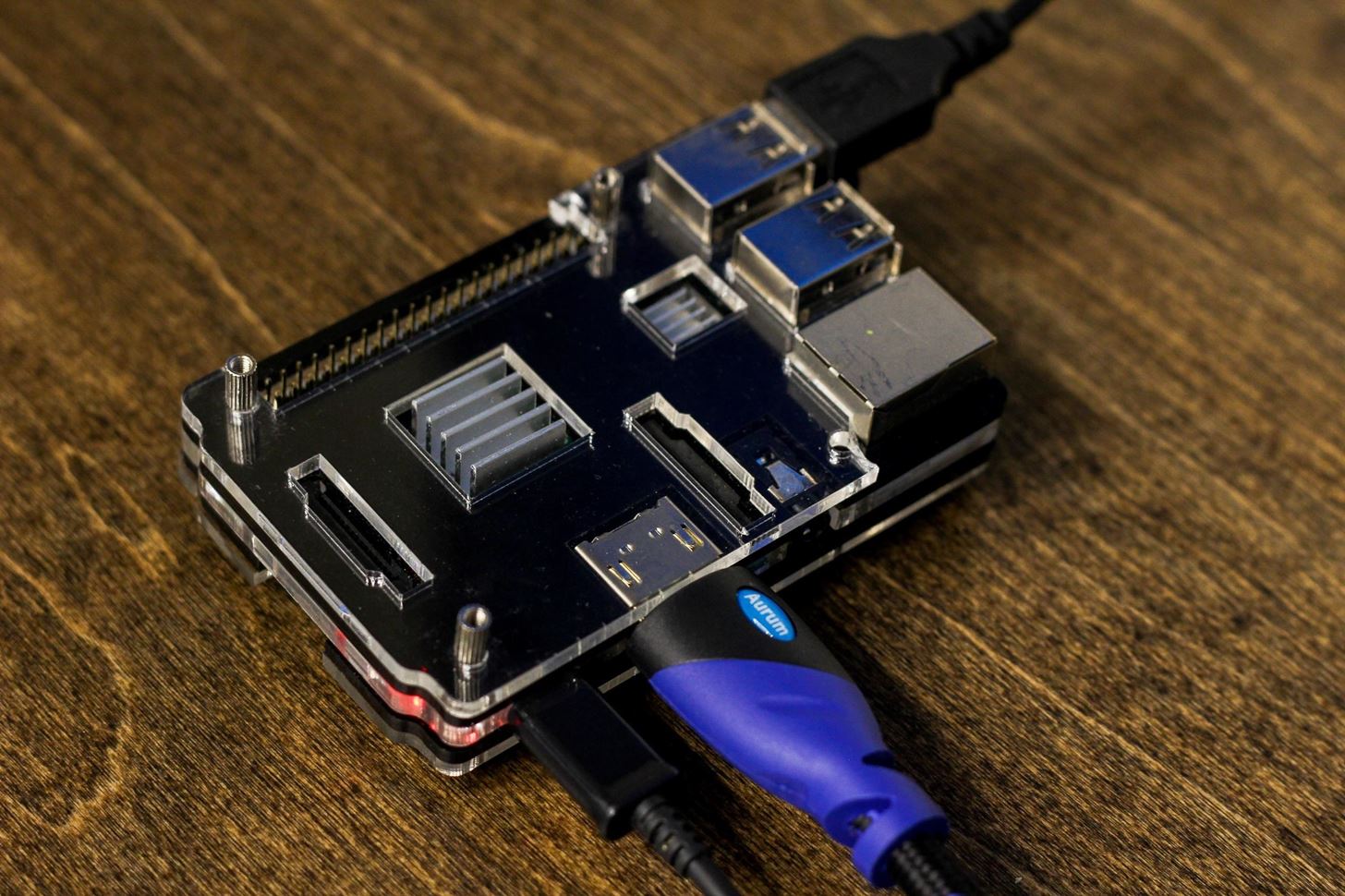
How to Hack Radio Frequencies: Hijacking FM Radio with a Raspberry Pi & Wire « Null Byte :: WonderHowTo
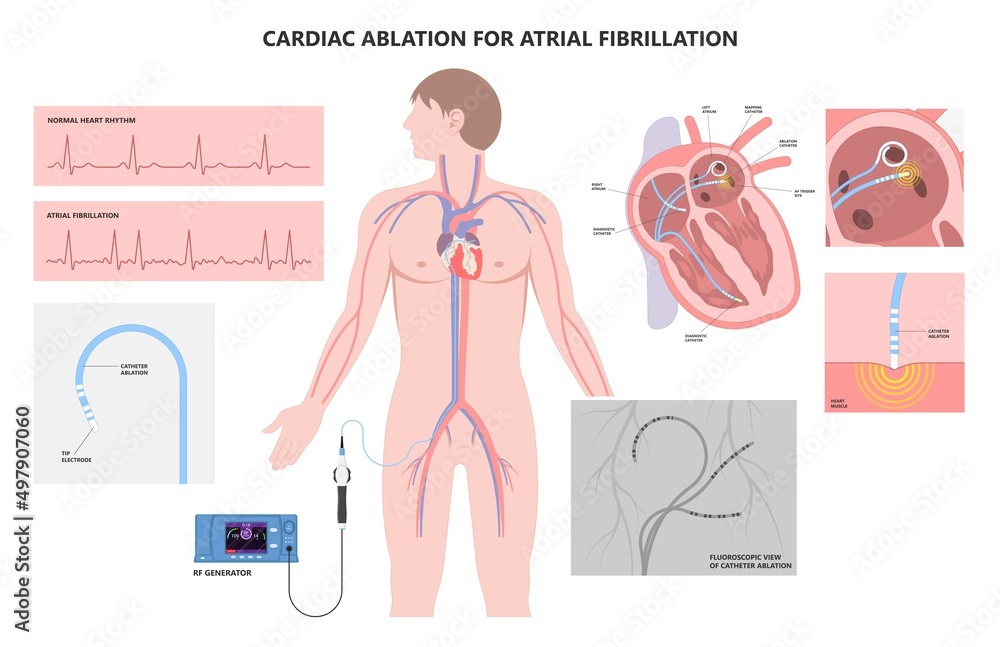
Vecteur Stock Cardiac catheter ablation treatment Atrial fibrillation rhythm problem minimally invasive procedure attack cath lab treat Coronary x-ray Radio frequency Sinus Ventricular SVT ECG ICD Radiofrequency AV | Adobe Stock
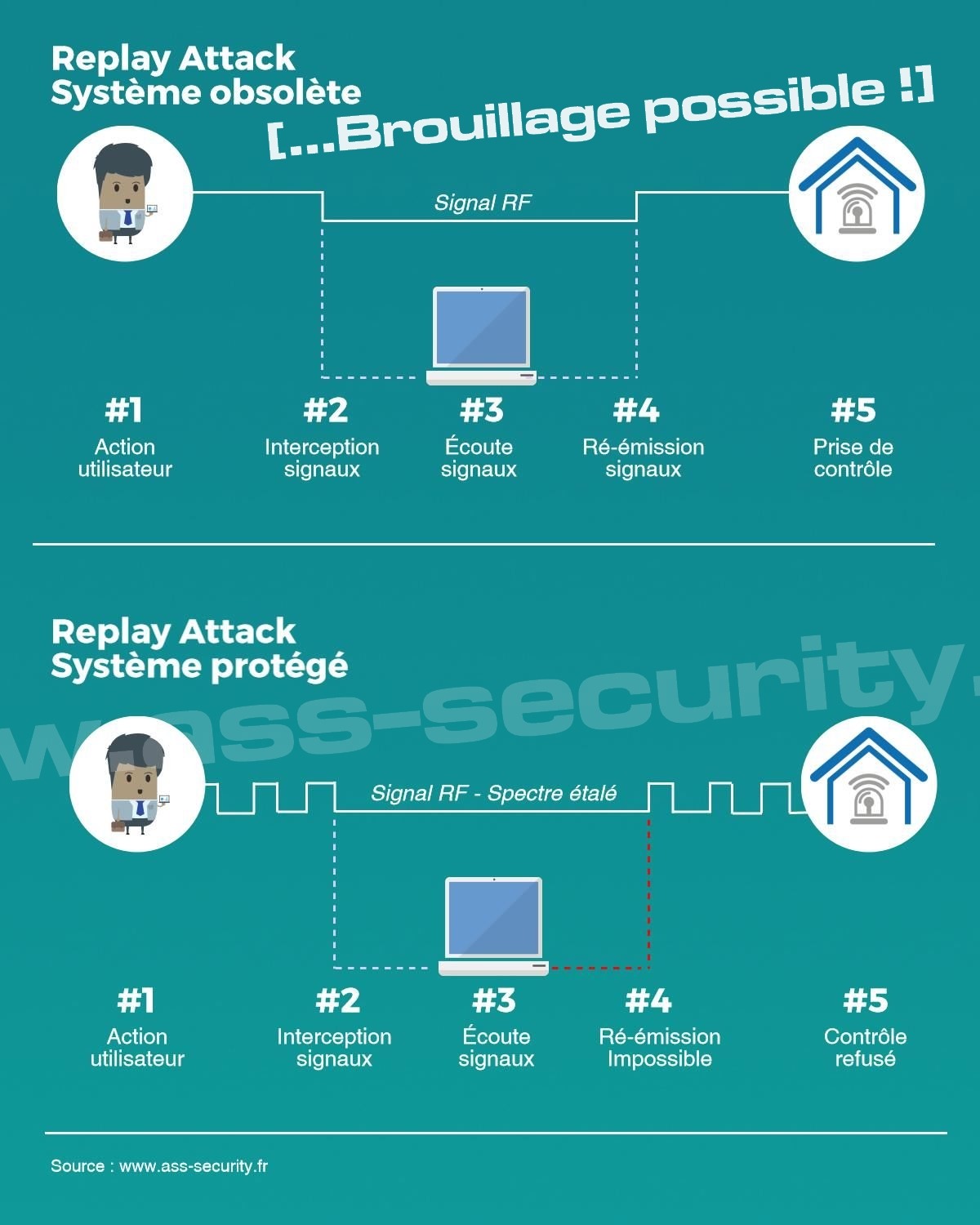
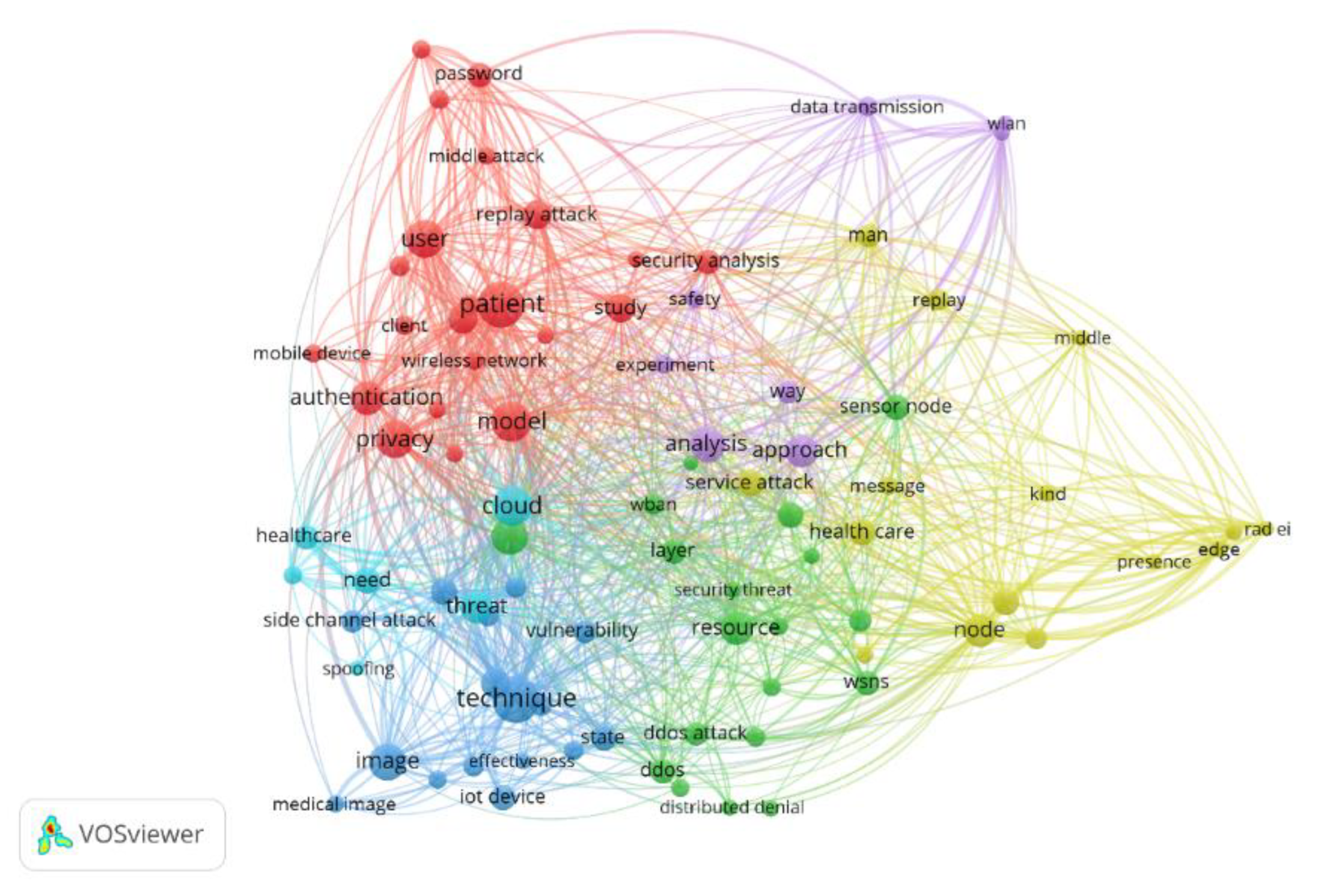
Dossier : Alarme sans-fil, Brouillage, Piratage d'une alarme Radio, Vulnérabilités, Perturbations...




_637280703542341277.png)